ZeroTrusted.ai SOAR Platform
AI-Powered Security Orchestration, Automation & Response
Version 3.0 | March 2026
232 AI Agents · 288 Tools · 6 Languages · FedRAMP High
Platform Modules
- Platform Overview
- Command Center
- Orchestration
- Automation
- Response
- AI Intelligence & Agent Management
- AI Security
- Deep AI System Testing
- AI CNO Platform
- Autonomous SOC
- Threat Detection Suite
- Compliance & Governance
- Sector-Specific Compliance
- Infrastructure & Deployment
- Security Best Practices
- API Reference
1. Platform Overview
ZeroTrusted.ai is an AI-powered Security Orchestration, Automation, and Response (SOAR) platform purpose-built for government and enterprise compliance. Version 3.0 integrates 232 specialized AI agents across 6 languages to deliver end-to-end security orchestration aligned with FedRAMP High, NIST SP 800-53 Rev 5, CMMC 2.0, and Zero Trust Architecture principles.
The platform provides comprehensive security capabilities spanning threat intelligence, vulnerability management, compliance automation, incident response, AI governance, counter-AI network operations (CNO), and autonomous SOC operations. It is designed to meet the rigorous requirements of federal agencies, defense contractors, financial institutions, and healthcare organizations operating under strict regulatory mandates.
Version 3.0 introduces significant new capabilities: Deep AI System Testing (a comprehensive AI evaluation framework with structured adversarial testing and evidence packaging), the AI CNO Platform with 12 counter-AI and Information Operations agents, an Autonomous SOC with 24/7 AI-driven triage, a global classification banner system for classified deployments, and the Unified Findings pipeline consolidating security findings across all scanning modules.
Key Capabilities
- 232 AI agents across 7 functional categories (security, compliance, AI governance, CNO, evaluation, intelligence, workforce)
- 288 tools across 33 categories with 97.3% coverage of manifest tool references
- 6 languages supported: English, Spanish, Japanese, French, German, Portuguese
- 14 compliance frameworks: FedRAMP High, CMMC 2.0, NIST SP 800-53r5, ISO 27001, SOC 2, HIPAA, PCI DSS, NERC CIP, NIST AI RMF, EU AI Act, Japan AI Governance, Brazil LGPD, DoD 8140 (DCWF), DISA STIG
- AI Firewall with DLP, prompt injection defense, content filtering, and rate limiting
- Global classification banner system supporting 8 levels from None through TOP SECRET//SCI
See the Platform in Action
Experience the full power of 232 AI agents working together to secure your enterprise.
Request a Demo View Pricing2. Command Center
The Command Center is the executive hub of the platform, providing unified situational awareness across all security operations, compliance posture, AI agent activity, and threat intelligence. All modules surface their most critical data here for rapid operator decision-making.
SOAR Dashboard
The SOAR Dashboard serves as the central command hub providing a unified operational view of all security activities. It aggregates real-time metrics from vulnerability scanners, compliance engines, incident response workflows, and AI agent operations into interactive visualizations with drill-down capability. Operators can monitor system posture at a glance with color-coded risk indicators, trend analysis charts, and automated alert prioritization.
Cross-Module Risk Integration
Cross-Module Risk Integration correlates security data from multiple platform modules to compute holistic risk scores. It combines vulnerability findings from SAST/DAST scanners, compliance gaps from control assessments, threat intelligence indicators, and POA&M status into a weighted risk matrix. This eliminates blind spots from siloed security tools and provides leadership with a single, defensible risk posture metric.
Unified Findings
A consolidated pipeline that aggregates security findings from all scanning, assessment, and AI agent modules into a single, normalized view. Findings from SAST, DAST, network scanning, STIG checks, threat intelligence, AI CNO operations, vulnerability assessments, and continuous monitoring are deduplicated, severity-normalized, and enriched with MITRE ATT&CK mapping and CVE/CWE identifiers.
- Aggregates findings from 12+ source types
- Severity normalization: Critical, High, Medium, Low, Informational
- MITRE ATT&CK TTP mapping and CVE/CWE enrichment
- Status lifecycle: Open → In Remediation → Resolved → Risk Accepted → False Positive
- One-click POA&M generation and export for ATO packages
Threat Intelligence
Aggregates, normalizes, and correlates threat data from multiple feeds including CISA KEV, NVD, MITRE ATT&CK, and commercial threat intelligence providers. Automated IOC enrichment, NIST control family mapping, and actionable intelligence briefs with STIX/TAXII interoperability.
Threat Intelligence Watchlist
Create and manage curated lists of IOCs, suspicious domains, IP addresses, and threat actor profiles. Watchlist entries are continuously monitored against incoming telemetry with automated alerts and integration into the Incident Response workflow.
Test Scheduler
Centralized scheduling of all security testing activities supporting 12+ test types: Pen & Vulnerability Testing, Red/Blue/Purple Team, SAST/DAST/Compliance Scan, AI CNO Operations, Information Operations, and Vulnerability/Network Scan — all integrated with the Unified Findings pipeline.
Continuous Monitoring
Real-time and scheduled security posture monitoring tracking MTTD, MTTC, and MTTR KPIs alongside FedRAMP ConMon compliance requirements. Automated alerts on threshold breaches, policy drift, or newly detected vulnerabilities with configurable alerting rules per control family.
Global Classification Banner System
For classified deployments, mandatory classification markings render at the top and bottom of every page viewport with color coding per classification level — from CUI (green) through TOP SECRET//SCI (yellow). Configurable via Platform Settings and persistent across sessions.
3. Orchestration
System Security Profiles
Define the security baseline configuration for each information system under management. Profiles capture system categorization (FIPS 199), authorization boundary definitions, applicable control baselines, and operational environment parameters. Multiple profiles can be maintained simultaneously for different authorization packages.
Asset Inventory Management
Comprehensive tracking of all hardware, software, and cloud resources within the authorization boundary. Automated discovery, configuration baselines, lifecycle state tracking, and audit-ready inventory reports with CMDB integration and SWID/CPE-compliant asset identifiers for SCAP compatibility.
Authorization Boundaries & Identity Access
Define and visualize system authorization boundaries aligned with NIST SP 800-18. Maps data flows, interconnection security agreements (ISAs), and identity access policies with role-based access control (RBAC), attribute-based access control (ABAC), and Zero Trust continuous authentication.
Supply Chain Risk Assessment
Evaluate third-party vendor and component risks per NIST SP 800-161 and the SECURE Software Development Framework. Software bill of materials (SBOM) management, vendor security posture tracking, single-source dependency identification, and automated alerts for newly disclosed supply chain vulnerabilities.
4. Automation
AI Document Generator
Automate the creation of System Security Plans (SSPs), Security Assessment Reports (SARs), and Plan of Action & Milestones (POA&Ms). AI synthesizes uploaded evidence, system configurations, and control implementation details into properly formatted compliance artifacts following FedRAMP, NIST, and DoD templates with version control.
SAST (Static Application Security Testing)
Static analysis of source code to identify security vulnerabilities, coding standard violations, and potential weaknesses before deployment. Multiple language support with customizable rule sets mapped to CWE identifiers and OWASP categories, including severity ratings and one-click remediation.
DAST (Dynamic Application Security Testing)
Runtime testing of web applications and APIs to discover vulnerabilities that manifest only during execution. Authenticated and unauthenticated scanning for OWASP Top 10 vulnerabilities, security headers, and TLS configurations — correlated with SAST findings for comprehensive application security coverage.
Network Scanning
Automated discovery and vulnerability assessment of network infrastructure including hosts, services, and configurations. Port scanning, service enumeration, OS fingerprinting, and CVE database mapping with continuous monitoring and differential reporting.
STIG Checker
Validate system configurations against DISA Security Technical Implementation Guides with automated assessment of hundreds of STIG controls across operating systems, databases, web servers, and network devices. CAT I/II/III severity classifications with XCCDF export for eMASS import.
Packet Capture
Network traffic analysis and forensic capture with filtered capture based on protocols, ports, and hosts. Real-time packet inspection, PCAP file export, and analysis for anomalous patterns, data exfiltration indicators, and protocol compliance violations.
AI Policy Generation Wizard
AI-assisted creation of comprehensive security policies aligned with NIST, ISO 27001, and organizational requirements — including acceptable use, incident response plans, data classification, and access control procedures with guaranteed policy consistency and regulatory alignment.
Patch Management
Track, prioritize, and orchestrate security patch deployment with risk-based priority scoring, approval workflows, and compliance reporting on patch currency against organizational SLAs.
Data Synchronization
Bidirectional data flows with SIEM systems, ticketing platforms, CMDB databases, and cloud security services. Configurable synchronization schedules with conflict resolution and full audit trails.
Automation Engine
Workflow orchestration framework for automated security playbooks with event-driven triggers, conditional branching, parallel execution, and external API integration. Pre-built templates for threat response, compliance evidence collection, and vulnerability remediation.
5. Response
Incident Response Management
End-to-end incident lifecycle tracking from detection through resolution and lessons learned. NIST SP 800-61 incident handling with automated classification, escalation workflows, evidence chain-of-custody, and post-incident reporting with real-time team coordination.
POA&M Tracker
Manage security findings, remediation plans, and milestone tracking per OMB A-130 requirements. Auto-generates POA&M entries from scan results, assessment findings, audit observations, and AI agent mission findings with remediation progress visibility and risk acceptance tracking.
Forensic Evidence Collection
Structured capture, preservation, and chain-of-custody management for digital evidence. Automated evidence gathering from system logs, network captures, memory dumps, and file system artifacts — all SHA-256 hashed, timestamped, and documented for legal and regulatory proceedings.
CP/IR Plan Testing
Test and validate Contingency Plans and Incident Response plans through tabletop exercises, functional tests, and full-scale exercises. Scenario libraries, exercise management tools, after-action report templates, and corrective action tracking that feeds back into plan improvements.
Team Security Assessments
Structured assessments of organizational security practices, personnel awareness, and procedural compliance with assessment templates, scoring rubrics, gap analysis, and trend tracking to inform training priorities.
Log Artifact Management
Centralized collection, parsing, normalization, and retention of security log data with multiple format support, advanced search and correlation, cryptographic signing for integrity, and retention policies compliant with NIST AU control family requirements.
6. AI Intelligence & Agent Management
The platform’s AI Intelligence layer manages 232 specialized AI agents organized across 7 functional categories. Each agent is defined by a capability manifest specifying its knowledge, skills, attributes (KSA), tools, guardrails, compliance frameworks, and required evidence artifacts. Agent QA scoring validates all 8 manifest fields with Grade A (100%) required for production operation.
AI Visibility & Traceability
Comprehensive observability into all AI model operations — tracking inputs, outputs, decision pathways, and confidence scores with full audit trails. Explainability reporting for regulatory compliance and bias detection through statistical analysis of model outputs across demographic categories.
AI Governance & Assurance
Organizational framework for responsible AI deployment: AI risk assessments, model approval workflows, ethical review processes, and compliance attestations aligned with NIST AI RMF, EU AI Act, and organizational governance policies.
AI Agent Management (232 Agents)
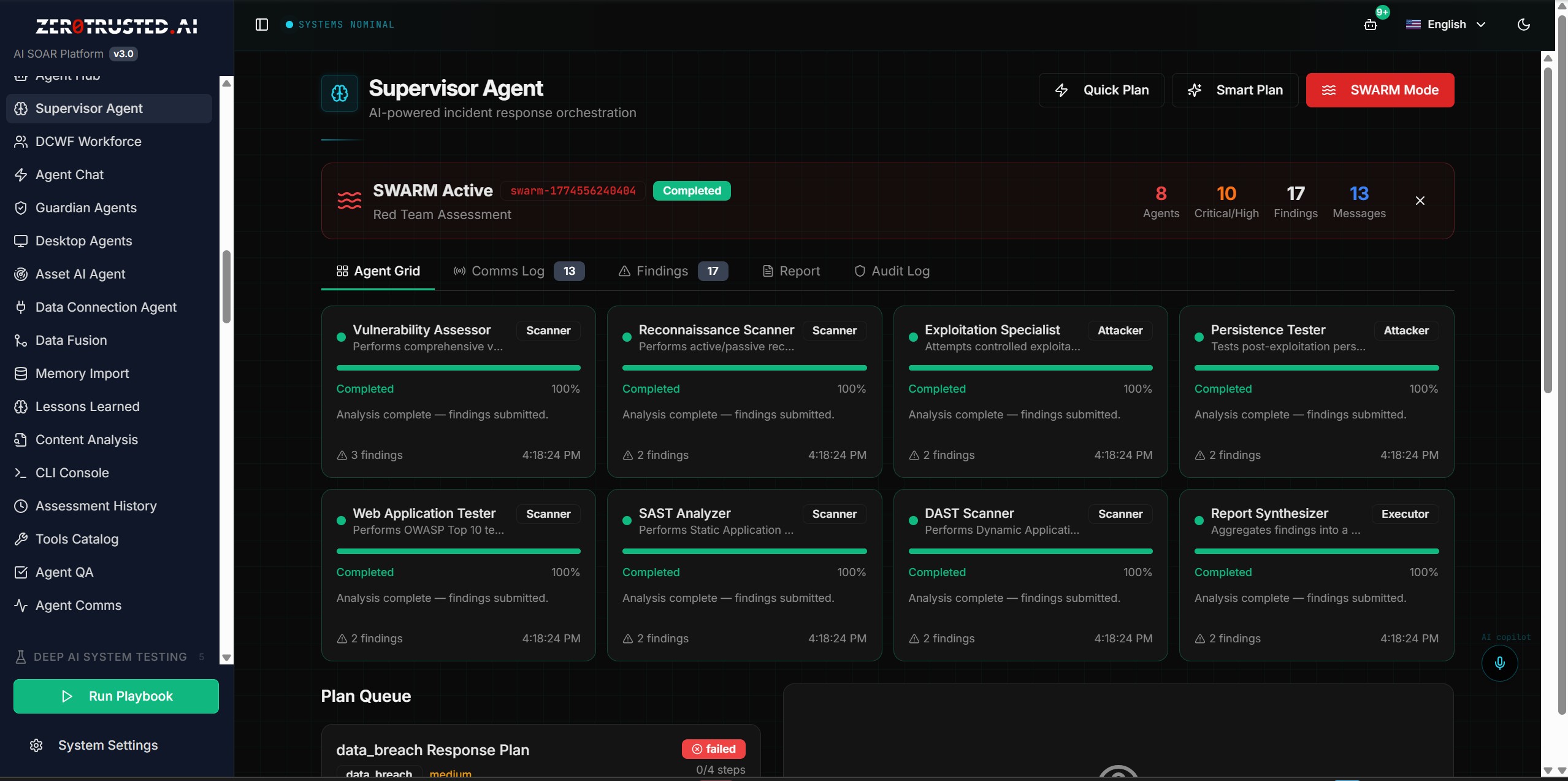
Orchestrate 232 specialized AI agents across 7 functional categories: Security Operations, Compliance & Governance, AI Governance, Counter-AI Network Operations (CNO), Deep AI System Testing, Intelligence & Workforce (DCWF 74 roles), and Autonomous SOC. Real-time agent status monitoring, task queue visibility, performance optimization, and mission tracking with WebSocket-streamed tool call events.
Agent QA Dashboard
Automated quality assurance scoring for all agents against 8 mandatory manifest fields: KSA, tools, emits, consumes, guardrails, requiredEvidence, complianceFrameworks, and description. Current status: 217 Grade A agents of 223 validated (97.3% pass rate).
AI Agent Chat Framework
Conversational interface for interacting with specialized AI agents. Query agents for security analysis, request automated actions, and receive contextual guidance with multi-turn conversations, context retention, and seamless handoff between specialist agents.
Supervisor Agent
Coordinates multi-agent workflows — decomposing complex security operations into subtasks, assigning to specialist agents, monitoring execution, and aggregating results with conflict prevention and resource allocation optimization.
Guardian Agents
Autonomous monitoring agents that continuously watch for security anomalies, policy violations, compliance drift, and emerging threats. Autonomous execution of predefined response actions or escalation to human operators based on severity.
Desktop Agent Platform (OpenClaw)
Lightweight agent runtime for endpoint environments — local vulnerability scanning, configuration assessment, evidence collection, and policy enforcement on desktop and server endpoints via encrypted channels within defined security boundaries.
AI Token Observability
Granular monitoring of token consumption across all AI model interactions. Usage tracking by agent, task type, model, and time period with cost attribution, budget alerting, prompt efficiency scoring, and model selection recommendations.
7. AI Security
AI Firewall
Comprehensive protection for AI model interactions through multiple security layers mapped to NIST SP 800-53 controls:
- Data Loss Prevention (DLP) — Detects PII, PHI, financial data, and classified content
- Prompt Injection Detection — Identifies and blocks adversarial prompt manipulation
- Content Filtering — Enforces organizational content policies on AI inputs and outputs
- Rate Limiting — Configurable request throttling per user, role, and API key
AI HealthCheck
Comprehensive AI model validation across 5 test categories: accuracy and reliability, security and robustness, fairness and bias, transparency and explainability, and privacy and data protection. Configurable acceptance thresholds, automated evidence pack generation, and continuous monitoring with regression detection.
AI Application Security Assessment
Evaluate AI-powered applications against OWASP Top 10 for AI/ML, NIST AI RMF, and MIT AI risk taxonomy. Identifies vulnerabilities specific to AI systems including model theft, training data poisoning, adversarial inputs, and output manipulation.
AI Guardrails
Enforce behavioral boundaries for all platform AI agents through 13 guardrail frameworks and 29 configurable policies covering hallucination prevention, data sovereignty, output sanitization, tool-use constraints, and ethical use boundaries. All enforcement events logged to the immutable audit trail.
AI WAF (Web Application Firewall)
Protection layer targeting the OWASP LLM Top 10 attack categories — inspecting AI inference traffic for prompt injection, insecure output handling, training data poisoning, model denial-of-service, and excessive agency exploitation with versioned, zero-downtime rule updates.
Ready to Secure Your AI Stack?
From AI Firewall to HealthCheck to Guardrails — protect every layer of your AI deployment.
Try a Live Demo Contact Sales8. Deep AI System Testing
A comprehensive AI evaluation framework providing structured, evidence-based validation of all platform AI agents. Five integrated modules cover the full evaluation lifecycle from benchmark definition through human adjudication, mission tracing, adversarial stress testing, and evidence package export for Authorizing Official (AO) submission. Six dedicated evaluation agents orchestrate all evaluations.
Benchmark Manager
Centralized registry for AI evaluation benchmarks with version-controlled definitions, configurable scoring rubrics with weighted dimensions, challenge set libraries (text, code, multi-turn, tool-use scenarios), scheduled automated runs with pass/fail thresholds, and full linkage to the evidence chain.
Human Review Workbench
Structured queue for human adjudication of AI agent outputs with rubric-guided scoring, annotation fields, Human-AI teaming comparisons, inter-rater reliability scoring, and blind review workflows. All adjudications are signed, timestamped, and included in evidence packages.
Agent Mission Trace
Full end-to-end timeline of AI agent mission execution capturing tool calls with input/output, approval events, memory references, retry sequences, tool-use quality scores, and execution timing. Real-time WebSocket streaming during active missions with exportable signed trace bundles.
Adversarial Testing
Structured attack scenarios and degraded operating conditions to validate robustness and safety:
- Attack Packs: Prompt injection, jailbreak, tool-abuse, unsafe-action, RAG attacks
- Degraded Conditions: Latency injection, tool denial, partial observability, rate limiting, network drops, DDIL simulation
- Failure mode classification with severity and remediation recommendations
- Guardrail effectiveness scoring across all active policies
Evidence Package Export
Single-bundle export containing all evaluation artifacts for AO review: benchmark results, human review adjudications, mission traces, adversarial test results, guardrail logs, and provenance chain. SHA-256 hash chain, OpenEval-v1.2 schema validation, DOCX/PDF export, and tamper-evident signing.
9. AI CNO Platform — Counter-AI & Info Ops
A dedicated console for degrading, disrupting, and denying adversary AI/ML-driven cybersecurity defenses via adversarial network-layer tactics. Hosts 12 specialized AI agents: 7 counter-AI agents targeting adversary ML systems and 5 AI Information Operations agents for narrative warfare, synthetic media detection, influence network analysis, and cognitive domain operations. All 12 agents score Grade A (100%).
Counter-AI Agents (7)
- AI CNO Platform Supervisor — Campaign orchestrator managing Phase 1–3 ROE, cross-agent coordination, and BDA aggregation
- Red AI Probe Agent — Black-box fingerprinting, decision boundary mapping, surrogate model construction, and transfer attack generation
- Signal Injection Specialist — False positive storm generation, false negative bypass, TLS obfuscation, and temporal injection scheduling
- MCP Intercept Agent — Deceptive MCP server registration, passive A2A traffic capture, and metadata poisoning
- Model Extraction Agent — Surrogate training, adversarial distillation, and offline evasion dataset generation
- BDA Analyst — Battle damage assessment via KL-divergence, KS-test, PSI metrics, and causal effect validation
- Temporal Attack Specialist — Phase-shifted injection campaigns, concept drift exploitation, and multi-update persistence
AI Information Operations Agents (5)
- IO Campaign Supervisor — Top-level IO campaign orchestrator for narrative, synthetic media, influence mapping, and cognitive domain operations
- AI Narrative Warfare Engine — Adversary ML effectiveness seeding via crafted narrative injection
- Synthetic Media Analyst — Deepfake attribution, synthetic media detection, and source analysis
- Influence Network Mapper — IO cluster analysis, social graph mapping, and coordinated inauthentic behavior detection
- Cognitive Domain Operations AI — Cognitive effect assessment, sentiment shift measurement, and audience vulnerability profiling
AI CNO Tool Catalog
46 specialized tools across 12 tool families covering the full counter-AI and information operations spectrum: red_ai.probe, signal.inject, mcp.intercept, model.extract, bda, temporal.attack, adaptive.ttp, narrative, influence, synthetic.media, cognitive, and io.campaign.
10. Autonomous SOC
24/7 AI-driven security operations with autonomous triage, containment, and escalation capabilities. Integrates six specialized sub-modules with an autonomous decision engine achieving 94%+ autonomous resolution rates while maintaining human-in-the-loop oversight for high-risk actions.
SIEM Integration Hub
Multi-platform SIEM ingestion from Splunk, Microsoft Sentinel, QRadar, and Elastic Security. Normalizes LEEF/CEF/JSON events, performs automated MITRE ATT&CK triage, and routes prioritized alerts. Processes 48,000+ events/sec with AI-powered TTP correlation and kill-chain reconstruction.
Identity Threat Detection & Response (ITDR)
Detects account compromise, credential stuffing, privilege escalation, lateral movement, and impossible travel patterns. Integrates with Active Directory, Entra ID, Okta, and CyberArk with MFA gap analysis and automated identity containment.
Email Security Gateway
AI-powered email threat protection: phishing, spear-phishing, BEC, executive impersonation, malicious attachments, and link analysis. DMARC/DKIM/SPF enforcement with ATP sandbox integration for zero-day attachment detonation.
Cloud Security Posture Management (CSPM)
Continuous multi-cloud posture assessment across AWS, Azure, and GCP. Auto-remediation of misconfigured resources below risk threshold with CIS Benchmark and FedRAMP boundary compliance validation.
Autonomous Decision Engine
AI-driven SOC orchestration across detection, investigation, containment, eradication, and recovery phases with 18 specialized autonomous agents. 94%+ autonomous decision rate with configurable escalation thresholds for high-risk actions.
SOC Communications Hub
Integrated communications: Slack/Teams alert routing, PagerDuty escalation, JIRA ticket creation, Zoom war room coordination, and executive briefing templates with severity-based escalation trees and runbook execution tracking.
11. Threat Detection Suite
UEBA (User & Entity Behavior Analytics)
AI-driven behavioral baseline profiling and anomaly detection across users, service accounts, and entities. Detects insider threats, compromised credentials, privilege abuse, and data exfiltration with continuously updated risk scores integrated with the Autonomous SOC.
Attack Surface Management (ASM)
Continuous external attack surface discovery: internet-exposed assets, shadow IT, certificate expiration, exposed credentials, and leaked data tracking with risk-ranked remediation priorities across managed and unmanaged surfaces.
Deception Technology
Honeypots, honey credentials, honey files, and honey tokens deployed to detect lateral movement and reconnaissance. Zero-false-positive by design with full session logging and immediate incident response escalation.
OSS Security Stack
Integrated open-source tool orchestration: Wazuh (host-based SIEM/IDS), Suricata (network IDS/IPS), Falco (runtime container security), Zeek (network monitoring), and osquery (endpoint telemetry) — all normalized into the Unified Findings pipeline.
12. Compliance & Governance
FIPS 199 Security Categorization
Federal information system categorization evaluating impact levels for confidentiality, integrity, and availability with compliant documentation and automatic security control baseline determination.
FedRAMP 20x KSI
Real-time monitoring of all 20 FedRAMP Key Security Indicator categories with automated evidence collection, ConMon reporting templates, and support for both Moderate and High baselines with control inheritance mapping.
NIST SP 800-53 Control Catalog
Comprehensive, searchable repository of all NIST SP 800-53 Rev 5 security and privacy controls linked to system profiles, POA&M items, and compliance evidence for full authorization package traceability.
SSP Control Export
Machine-readable System Security Plan exports in OSCAL, OpenControl, and JSON formats with control implementation descriptions, responsible roles, implementation status, and evidence references.
GIS Compliance Map
Geographic visualization of regulatory compliance requirements across jurisdictions — displaying applicable regulations, data residency requirements, and compliance status on an interactive world map.
SCAP Content Repository
Security Content Automation Protocol management: CVE, CCE, CPE, CVSS, OVAL, XCCDF, and CWE content with automated feed synchronization integrated into vulnerability management and compliance reporting.
13. Sector-Specific Compliance
Banking & Financial Compliance
SOX internal controls, PCI DSS payment card security, and GLBA financial privacy provisions with pre-built control mappings and automated evidence collection templates.
Healthcare & HIPAA
HIPAA Security Rule, Privacy Rule, and Breach Notification compliance management with risk assessment tools, BAA management, breach notification workflow automation, and administrative/physical/technical safeguard tracking.
Government & FISMA
Full ATO lifecycle under FISMA: system categorization, control selection, assessment, authorization, and continuous monitoring aligned with NIST RMF steps and OMB reporting requirements.
Energy & NERC CIP
CIP-002 through CIP-014 cybersecurity compliance for energy sector organizations covering electronic security perimeters, personnel training, incident reporting, and supply chain risk management.
EU AI Act Compliance
Risk classification tools, conformity assessment checklists, transparency obligation tracking, and documentation templates for high-risk AI system deployment under the EU Artificial Intelligence Act.
Japan AI Governance
Compliance with Japan’s APPI, METI AI governance guidelines, and MIC AI frameworks with governance documentation templates and regulatory mapping.
Brazil LGPD & AI Regulation
Data protection impact assessments, consent management, cross-border transfer documentation, and ANPD reporting for Brazil’s Lei Geral de Proteção de Dados compliance.
Fraud Detection
AI-driven fraud detection using behavioral analytics, anomaly detection, and pattern recognition integrated with the Incident Response workflow for automated investigation.
AML/KYC Compliance
Anti-Money Laundering and Know Your Customer management: transaction monitoring, SAR reporting, CDD workflows, and sanctions screening aligned with FinCEN, FATF, and local regulations.
Insurance Compliance
Cyber insurance risk assessment, NAIC model law requirements, state-specific regulations, and reinsurance treaty security requirements with pre-built assessment templates.
14. Infrastructure & Deployment
Kubernetes Security Assessment
38 automated security checks across cluster configuration, network policies, pod security, RBAC authorization, secrets management, and container runtime security — CIS Kubernetes Benchmark aligned.
Deployment Options
Automated installation and configuration for multiple environments:
- On-Premises — Kubernetes with NGINX Ingress, cert-manager, and CloudNativePG
- AWS — EKS with ALB, RDS PostgreSQL, and Secrets Manager
- Azure — AKS with Application Gateway, Azure Database for PostgreSQL, and Key Vault
- GCP — GKE with Cloud Load Balancing, Cloud SQL, and Secret Manager
Identity Management (IDAM) & Zero Trust Identity
Six authentication providers: Local (RBAC), LDAP/Active Directory, OpenID Connect, SAML 2.0, DoD CAC (smart card with mutual TLS), and Federal PIV (FPKI). Multiple simultaneous providers with configurable priority, group-to-role mapping, MFA enforcement, and session management. Zero Trust enforcement delivers continuous verification with identity-based micro-segmentation, device posture validation, and least-privilege access.
DRM License Management
Digital rights and licensing management with utilization monitoring, expiration tracking, entitlement boundaries, and procurement planning alerts.
Reports Module
PDF, DOCX, and XLSX exports with pre-built templates for executive summaries, compliance status, vulnerability assessments, incident reports, audit findings, and AI evaluation packages. Custom report building with configurable data sources and visualizations.
15. Security Best Practices
- Implement Zero Trust Architecture — Never trust, always verify. Enforce continuous authentication and least-privilege access for all users, devices, and services.
- Maintain Continuous Monitoring — Deploy real-time security monitoring with automated alerting for anomalies, policy violations, and emerging threats.
- Automate Compliance Evidence Collection — Use automated tools to continuously gather, validate, and organize compliance evidence.
- Practice Defense in Depth — Layer multiple security controls including network segmentation, endpoint protection, application security, and data encryption.
- Conduct Regular Security Assessments — Perform periodic vulnerability scans, penetration tests, configuration audits, and risk assessments.
- Enforce Strong Identity & Access Management — Implement MFA, RBAC, privileged access management, and regular access reviews.
- Maintain Incident Response Readiness — Develop, test, and maintain IR and contingency plans with regular exercises.
- Secure the AI Supply Chain — Validate AI model provenance, monitor for data poisoning, and maintain AI governance documentation.
- Validate AI Agents Continuously — Run regular QA evaluations against all 8 manifest fields. Maintain Grade A status for all production agents.
- Apply Classification Controls — Configure classification banners for classified deployments and review during every ATO reauthorization cycle.
16. API Reference
The ZeroTrusted.ai SOAR platform exposes a RESTful API for integration with external systems and automation workflows. All endpoints require authentication and support JSON request/response formats.
Endpoints
- GET /api/profiles — Retrieve system security profiles with FIPS 199 categorization and control baselines
- GET /api/assets — Retrieve asset inventory with configuration and lifecycle data
- GET /api/vulnerabilities — Retrieve SAST, DAST, and network scan findings with CVE mappings
- GET /api/poam — Retrieve POA&M items with status, milestones, and risk acceptance decisions
- POST /api/incidents — Create incident records with classification, severity, and response actions
- GET /api/ssp/controls-export — Export SSP controls in OSCAL, OpenControl, or JSON format
- GET /api/unified-findings — Retrieve consolidated findings from all scanning modules
- GET /api/ai-agents — Retrieve all 232 AI agent records with manifest data and QA scores
- POST /api/ai-agents/:id/mission/start — Start an AI agent mission with task parameters
- GET /api/ai-agents/qa/report — Retrieve Agent QA report with grades and summary statistics
- GET /api/threat-intel/findings — Retrieve threat intelligence with STIX/TAXII enrichment
- GET /api/continuous-monitoring/metrics — Retrieve MTTD, MTTC, MTTR, and ConMon status
Start Securing Your Enterprise AI Today
232 AI agents. 288 tools. 14 compliance frameworks. One unified platform.
Request a Demo Try Live Demo