
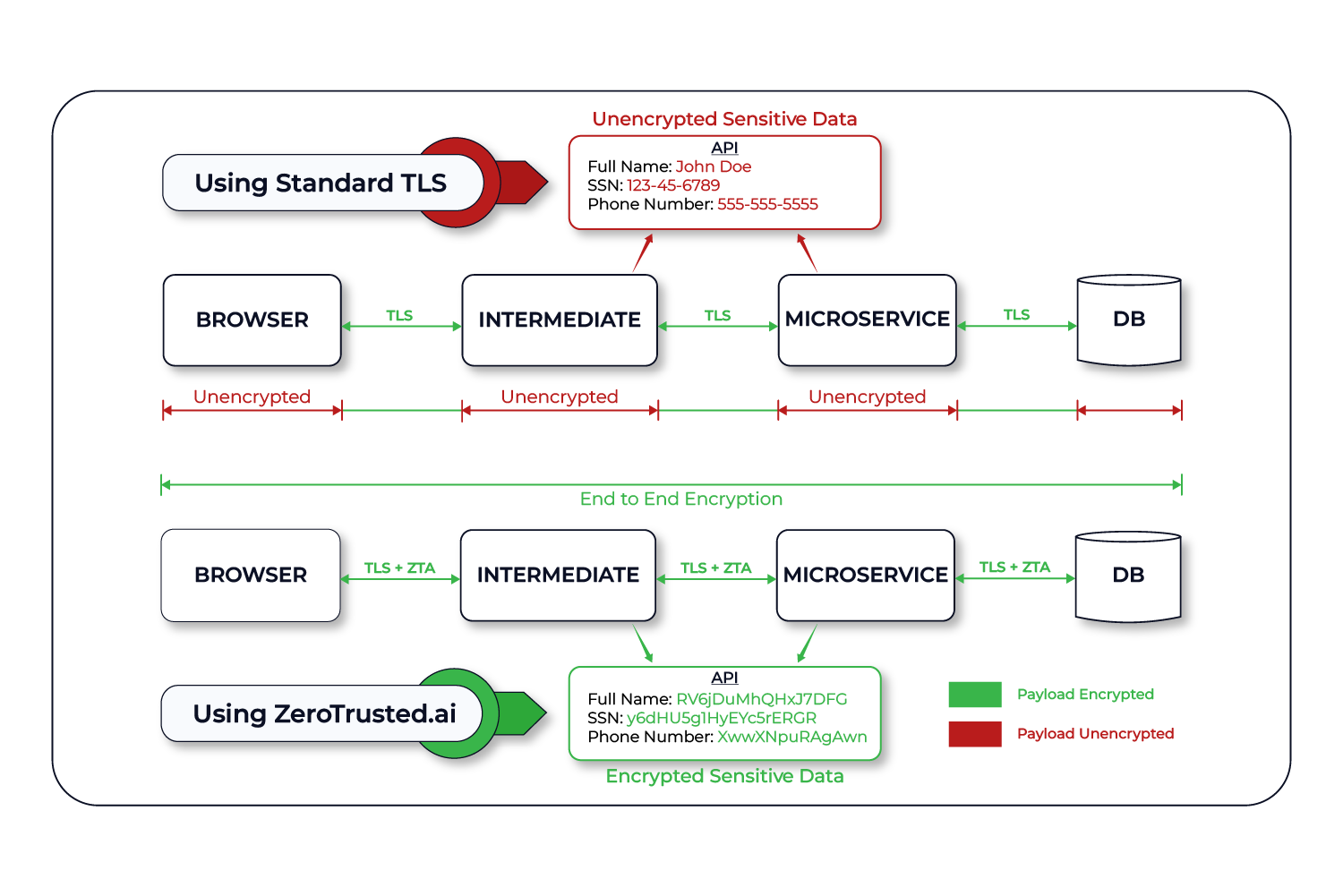
ZeroTrusted.ai’s End to End Encryption (E2EE) for web applications and APIs ensure secure data transfer by making it inaccessible to third parties during transmission. With E2EE, the sender encrypts the data, and only the designated recipient can decrypt it. This prevents unauthorized access or manipulation by ISPs, hackers, or other intermediaries.
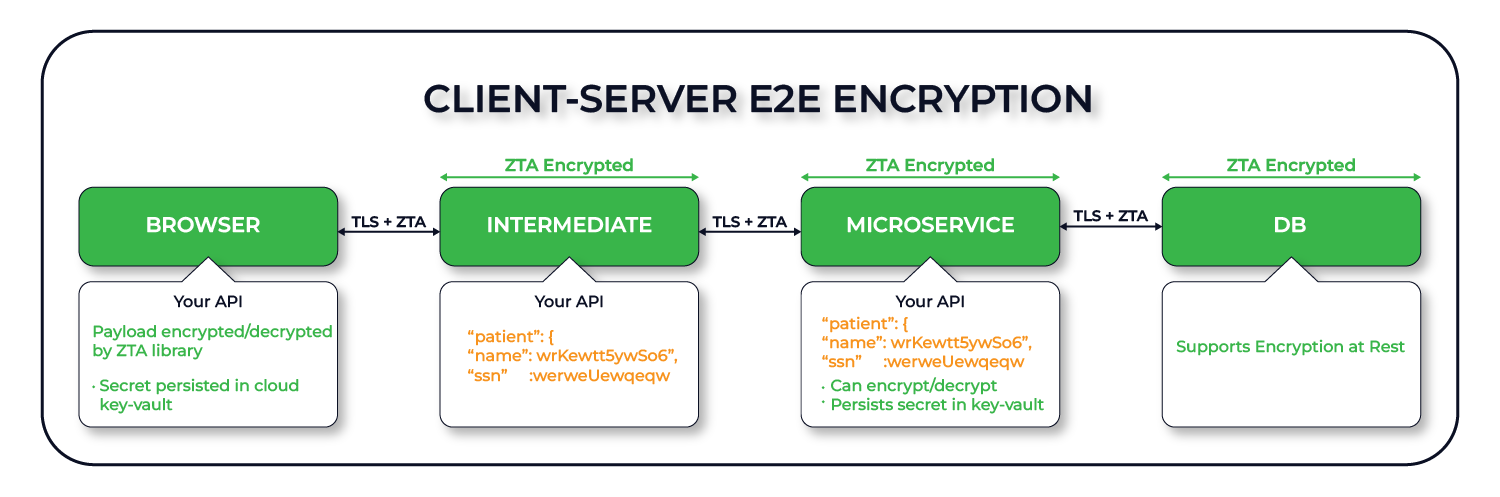
Client-Server End-to-End Encryption ensures that only the client (end-user) and the backend server can decrypt content. In otherward, users will be able access and view their data in decrypted format through browser or app, while associated backend servers or API microservices have the ability to also decrypt data as needed.
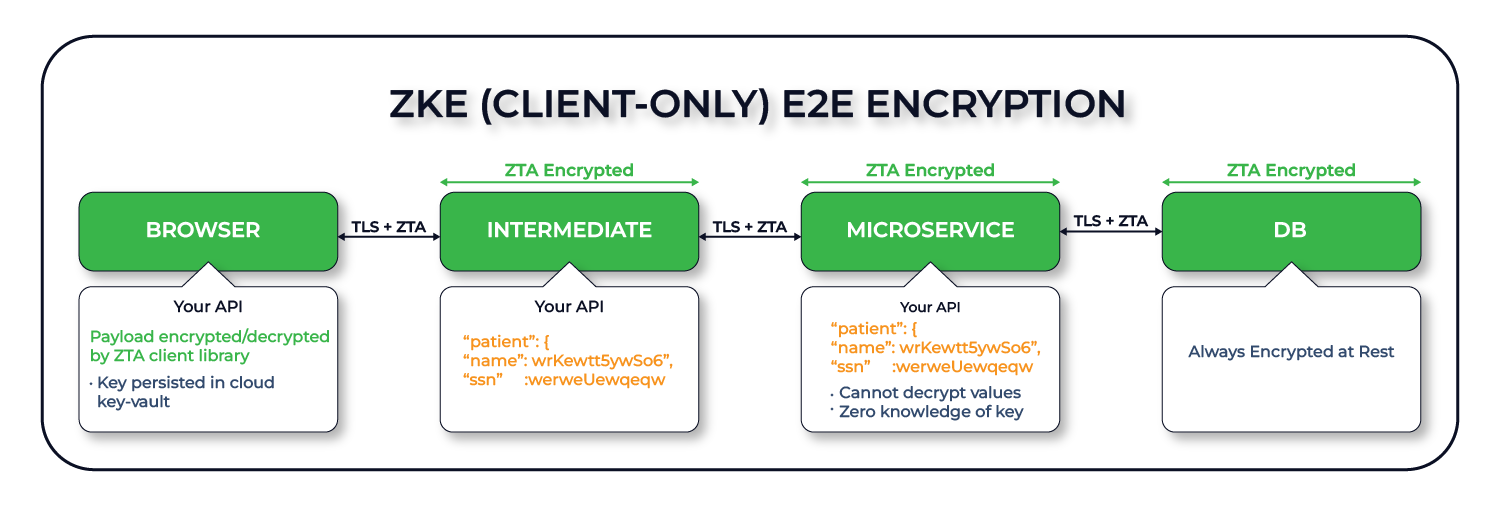
Zero Knowledge End-to-End Encryption ensures that only the client (end-user) can decrypt content. Users will be able access and view their data in decrypted format through browser or app. However, backend servers and API microservices do not have the ability to decrypt data. The data will be persisted in encrypted format.
Web3.Storage is the easiest way to build on the decentralized web from hackathon projects to production code at scale.
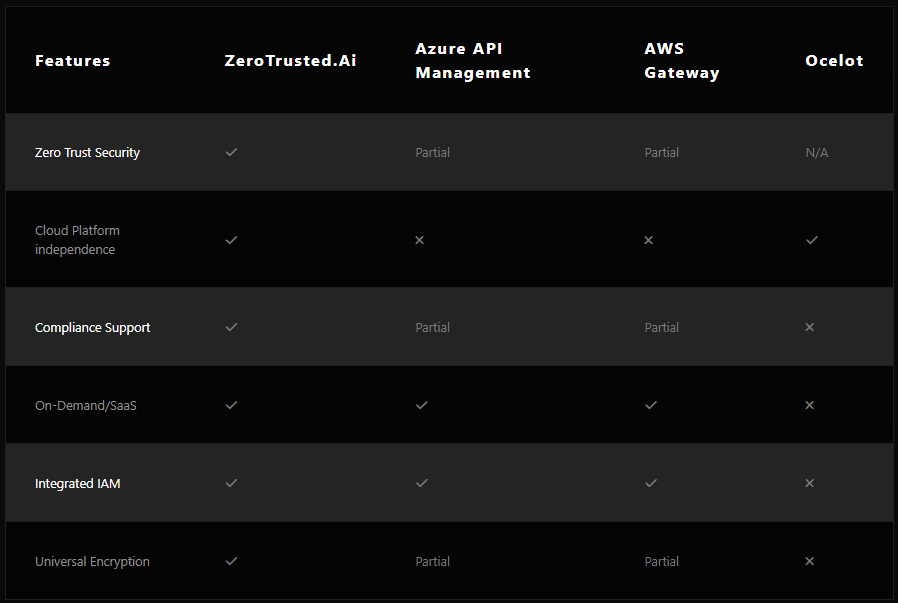
At ZeroTrusted.ai, we are committed to providing the highest level of security for your infrastructure.
Contact us today to learn how our innovative technologies and machine learning can help you achieve true Zero Trust Security.